Beyond the Hype: Empirical Analysis of Matter Standard’s Security and Privacy
Authors: Andrew Losty, Tianrui Hu, Daniel J. Dubois, Narmeen Shafqat, Aanjhan Ranganathan, David Choffnes, Anna Maria Mandalari
Venue: Internet Measurement Conference (IMC ’26), October 12–16, 2026, Karlsruhe, Germany
ACM ISBN: 979-8-4007-2327-8/26/10
DOI: https://doi.org/10.1145/3777912.3809142
Cync Matter Plug (Security Analysis)
Linkind Matter Plug (Privacy Evaluation)
Tuya Matter Plug (Traffic Behaviour Study)
Abstract
The rapid growth of the Internet of Things (IoT) has created fragmented smart home ecosystems, with platforms such as Apple Home, Google Home, and Samsung SmartThings historically relying on proprietary protocols and device-specific implementations that limited interoperability.
The Matter standard defines a common, secure application-layer framework enabling cross-platform interoperability for Internet of Things (IoT) devices. It is developed under the Connectivity Standards Alliance (CSA), an industry consortium comprising more than 860 member organizations.
This study empirically analyzes Matter and non-Matter ecosystems, focusing on security and privacy. We evaluate 25 Matter devices and 14 non-Matter devices with comparable functionality, examining network traffic during commissioning, device control, and data transmission.
Our evaluation shows that Matter improves security and privacy through AES-128-CCM encryption, device attestation, and secure commissioning. Its local-first design further reduces cloud dependency and limits data exposure.
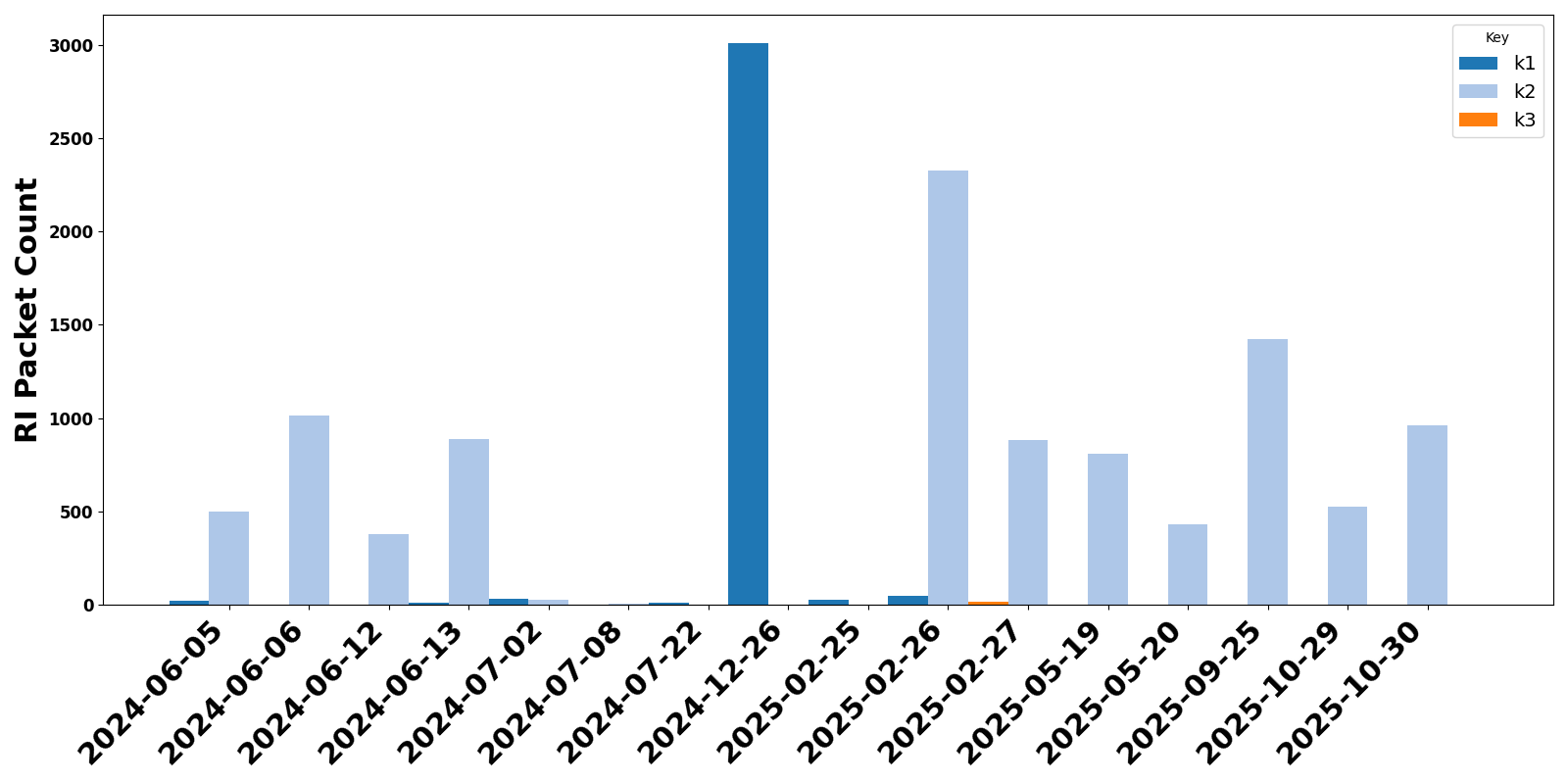
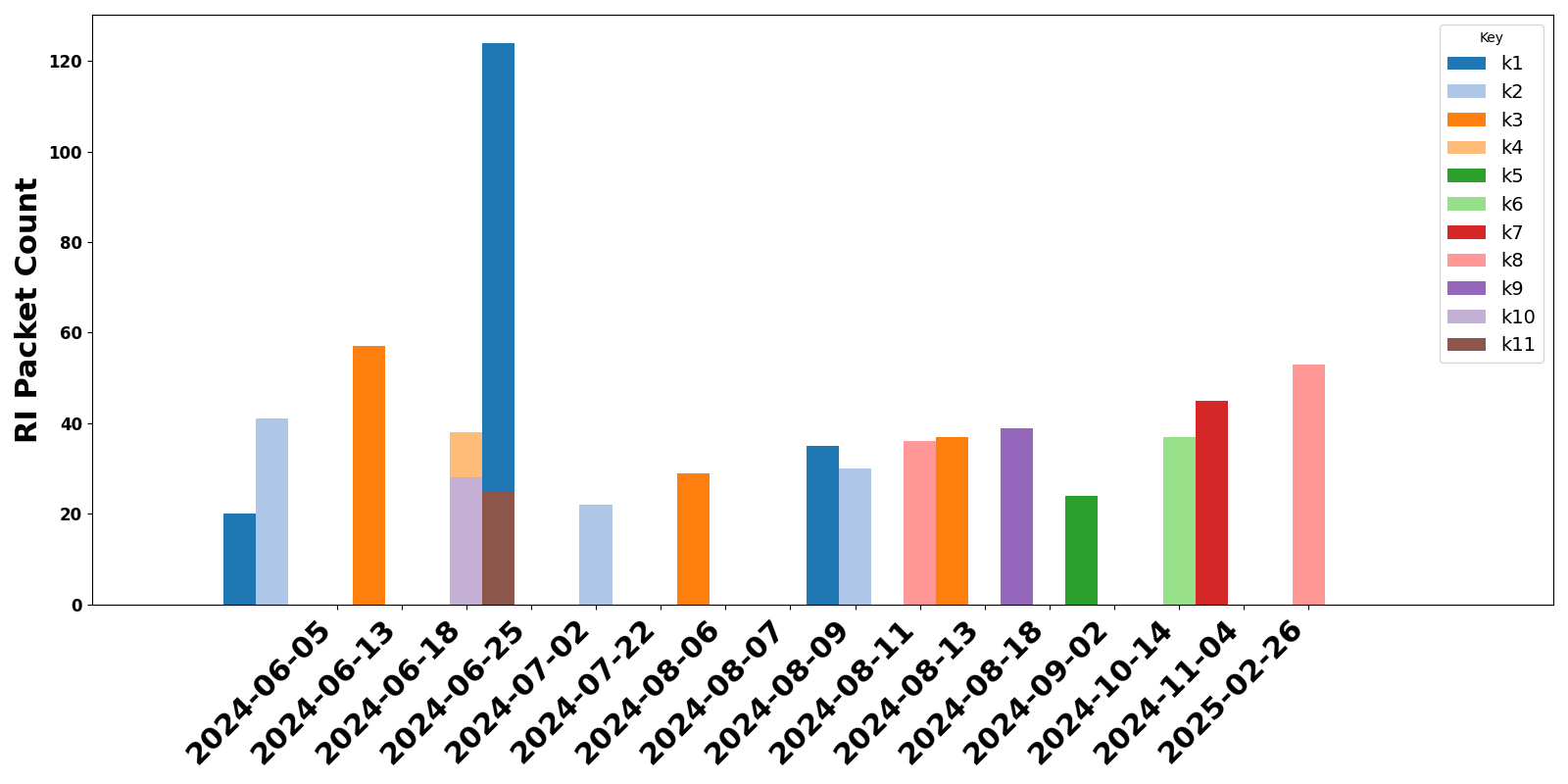
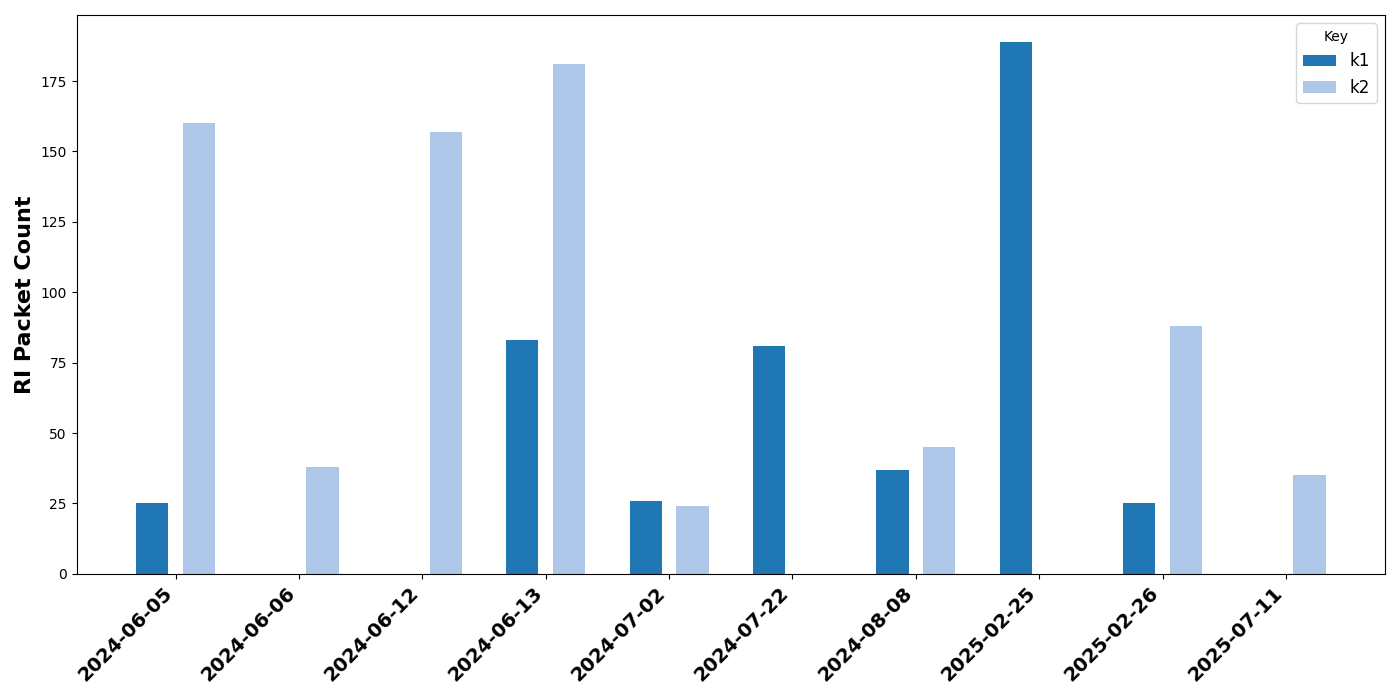
However, we identify several risks. Persistent multicast DNS broadcasts reveal detailed device metadata, and rotating key identifiers are inconsistently implemented, with some devices failing to renew keys for extended periods.
We also observe ecosystem-specific differences in commissioning behavior. In addition, many devices maintain persistent connections to vendor or third-party cloud services.
Firmware maintenance is inconsistent, as most devices in our study run early versions of Matter and do not receive updates over the observation period.
Finally, traffic patterns in encrypted unicast communication can still reveal device types and user activities to an in-network adversary.