From Lookup to Lockdown: DNS Guidelines for Securing IoT Ecosystems
Authors: A. Losty, A.K. Mishra, M. Cunche, A. M. Mandalari
Venue: IEEE Internet of Things Journal
Published in: IEEE Internet of Things Journal (Early Access)
DOI: 10.1109/JIOT.2026.3680083
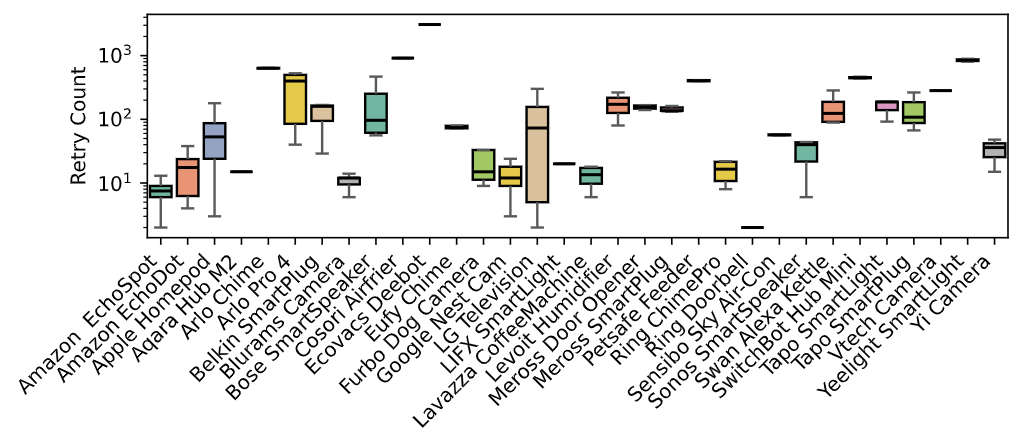
DNS Retry Guidelines
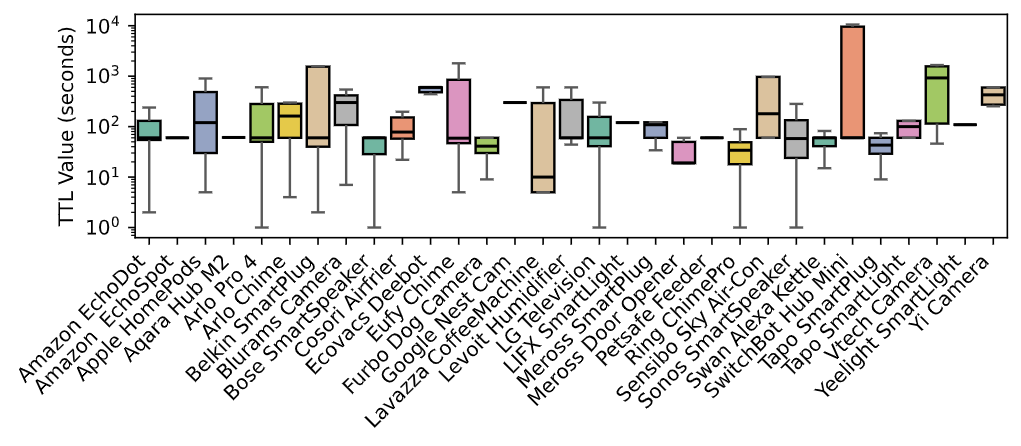
DNS TTL Guidelines
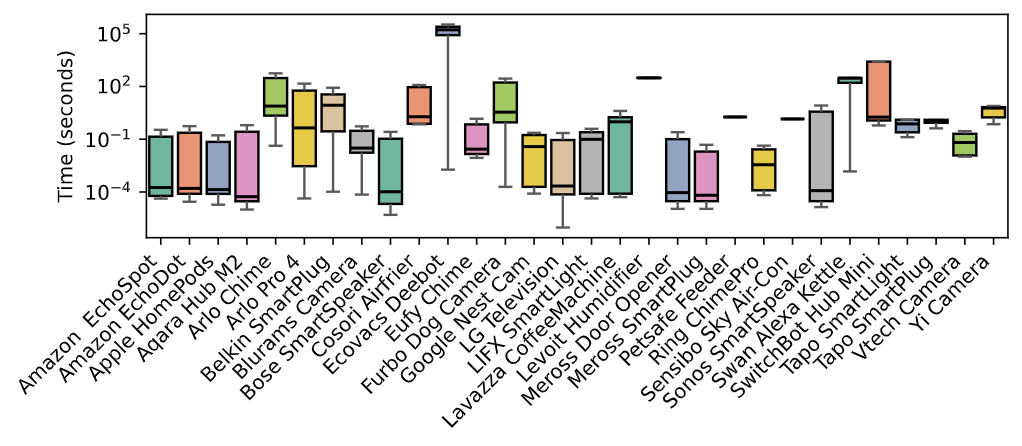
DNS IQT Guidelines
Abstract
The Domain Name System (DNS) serves as a fundamental component of Internet infrastructure; however, its frequently overlooked role in consumer Internet of Things (IoT) ecosystems exposes significant security vulnerabilities and operational challenges.
This paper analyzes DNS behavior in consumer IoT devices and reveals widespread inconsistencies that undermine operational efficiency, resilience, and security.
We construct a representative testbed spanning a heterogeneous set of IoT devices and employ both passive traffic monitoring and active experimentation to identify vulnerabilities, including cache poisoning, predictable transaction IDs, non-randomized source ports, and limited adoption of secure DNS protocols such as DNS-over-HTTPS (DoH), DNS-over-TLS (DoT), and Domain Name System Security Extensions (DNSSEC).
We observe erratic operational patterns, such as excessive querying, poor adherence to TTL values, and overreliance on hard-coded resolvers, that amplify exposure to fingerprinting and denial-of-service attacks.
Our findings demonstrate a concerning lack of standardized DNS practices across the IoT ecosystem.
We conclude by proposing actionable guidelines to harden DNS handling in IoT devices and improve security, interoperability, and network stability as the consumer IoT landscape continues to expand.