Research
Our research focuses on securing IoT systems across smart homes, healthcare, and industrial environments. We develop innovative solutions to address emerging threats and privacy challenges in connected ecosystems.
Published Papers
11 itemsSelected peer-reviewed papers, demos, and workshop publications related to IoT security in smart homes, healthcare, and industrial environments.
2026
From Lookup to Lockdown: DNS Guidelines for Securing IoT Ecosystems
A. Losty, A.K. Mishra, M. Cunche, A. M. Mandalari
Venue: IEEE Internet of Things Journal
Cybersecurity of Linear Accelerators in Radiation Oncology Beyond Ransomware
M. Alhussan, A. Alhussan, N. Chng, F. Boem, A. M. Mandalari
Venue: Radiotherapy and Oncology - Journal of the European Society for Radiotherapy and Oncology and affiliated to the Canadian Association of Radiation Oncology
An Analysis of Matter IoT Security Against International Standards and Regulatory Framework
A. Losty, A. M. Mandalari
Venue: Proc. Network and Distributed System Security Symposium (NDSS) / SDIoTSEC Workshop
2025
Hacking Health: Unveiling Vulnerabilities in BLE-Enabled Wearable Sensor Nodes
M. Alhussan, F. Boem, S. Ghoreishizadeh, A. M. Mandalari
Venue: Proc. 2025 IEEE International Symposium on Circuits and Systems (ISCAS)
Big Help or Big Brother? Auditing Tracking, Profiling, and Personalization in Generative AI Assistants
Yash Vekaria, Aurelio Loris Canino, Jonathan Levitsky, Alex Ciechonski, Patricia Callejo, Anna Maria Mandalari, Zubair Shafiq
Venue: 34th USENIX Security Symposium
Towards Operational and Security Best Practices for DNS in the Internet of Things
A. Losty, A. M. Mandalari, A. K. Mishra, M. Cunche
Venue: ANRW 2025 (Applied Networking Research Workshop)
Intelligent Detection of Non-Essential IoT Traffic on the Home Gateway
Palmese, Fabio; Mandalari, Anna Maria; Haddadi, Hamed; Enrico Cesare Redondi, Alessandro
Link: arXiv PDF
2024
Enabling Lawful Interception in Environments Protected by IoT Safeguard
Aurelio Loris Canino, Gianluca Lax
Link: Springer
Hacking Health: Unveiling Vulnerabilities in Wireless Wearable Sensors
M. Alhussan, F. Boem, S. Ghoreishizadeh, A. M. Mandalari
Venue: Proc. IEEE BioSensors Conference (2024)
Demo: From Eavesdropping to Exploitation: Exposing Vulnerabilities in BLE-Enabled Wearable Medical Devices
M. Alhussan, F. Boem, S. Ghoreishizadeh, A. M. Mandalari
Venue: 21st Intl. Conf. on Embedded Wireless Systems and Networks (EWSN)
PhD School: From Eavesdropping to Exploitation: Exposing Vulnerabilities in BLE-Enabled Wearable Medical Devices
M. Alhussan, F. Boem, S. Ghoreishizadeh, A. M. Mandalari
Venue: PhD School at EWSN (2024)
An Investigation of Matter Smart Home Mechanisms to Mitigate Denial-of-Service (DoS) Attacks
A. Losty, A. M. Mandalari
Venue: PhD School at EWSN (2024)
Research Posters

From Satellites to SIMs: A Layered Taxonomy of Network Shutdown Circumvention Technologies
Mapping resilient communication solutions against adversarially-imposed network shutdowns.
View Poster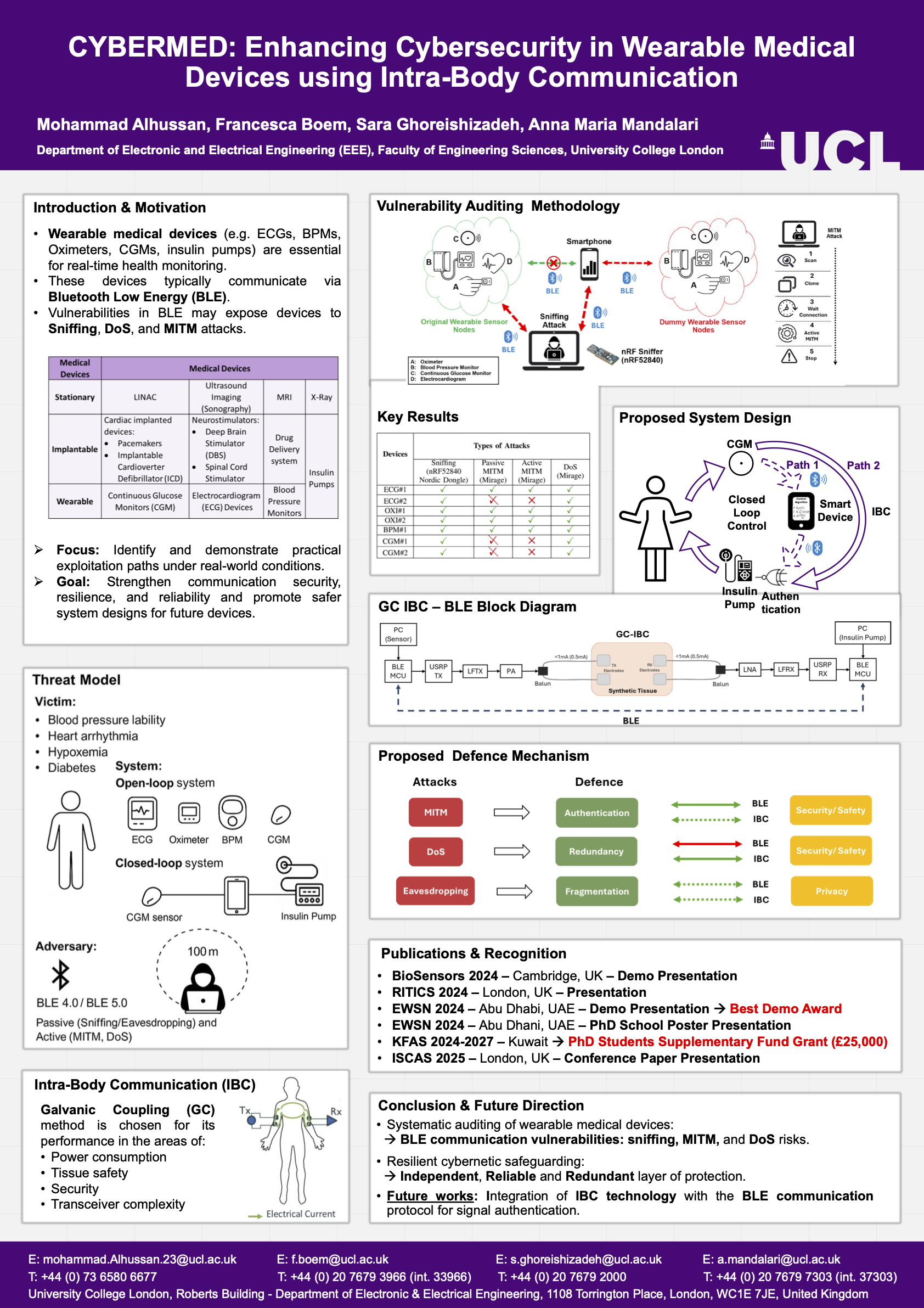
CYBERMED: Enhancing Cybersecurity in Wearable Medical Devices using Intra-Body Communication
Developing intra-body communication (IBC) as a secure alternative to vulnerable BLE in medical wearables, addressing sniffing/MITM/DoS risks while maintaining clinical functionality
View Poster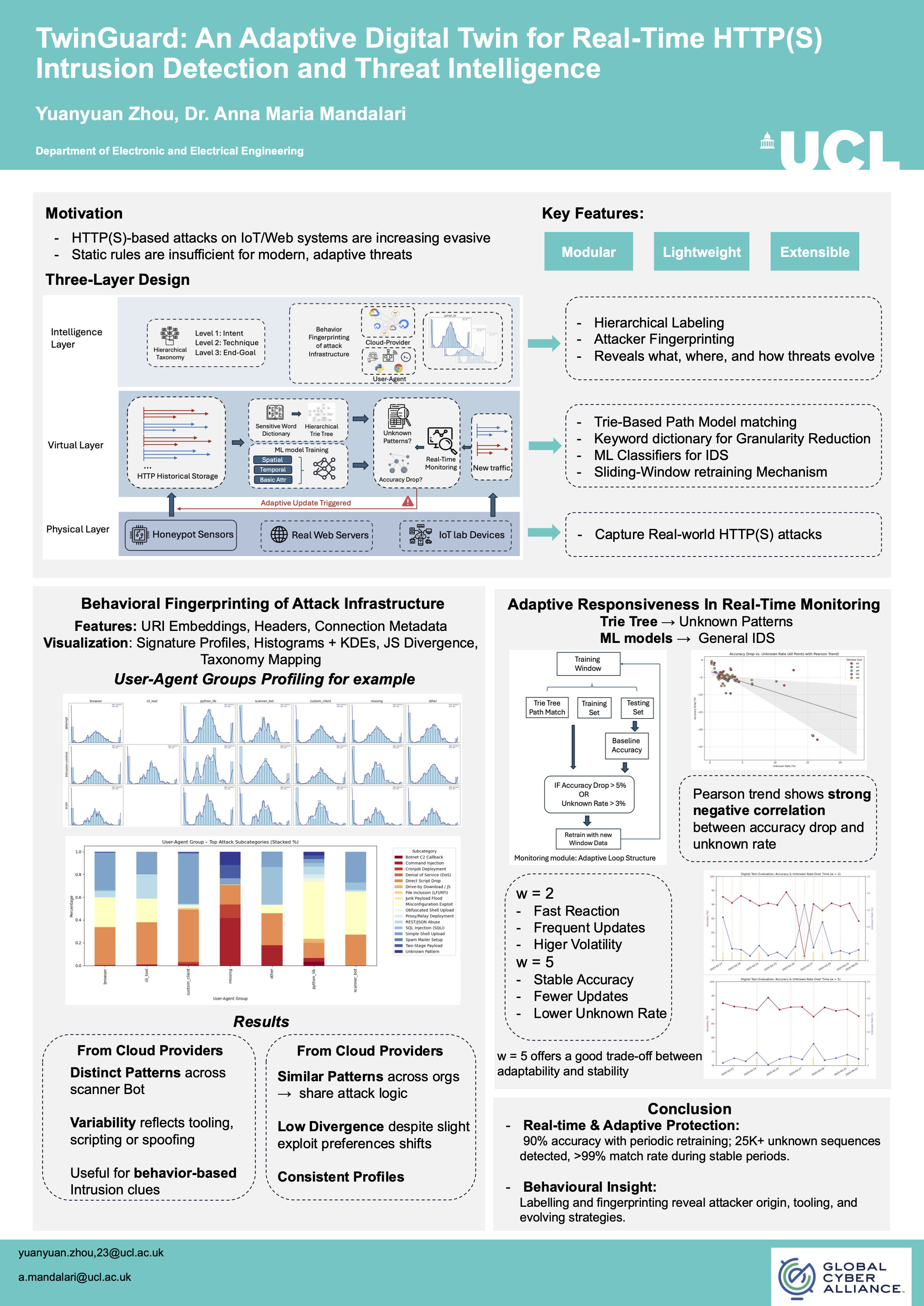
TwinGuard: An Adaptive Digital Twin for Real-Time HTTP(S) Intrusion Detection and Threat Intelligence
TwinGuard is an adaptive digital twin system for real-time HTTP(S) intrusion detection. It combines trie-based path modeling, behavioral fingerprinting, and machine learning to detect evolving threats with 90% accuracy. Key features include dynamic retraining, attacker infrastructure profiling, and granular traffic analysis—revealing attack origins, tools, and strategies.
View Poster